Solar Group
cybersecurity architect
850
significant companies in Russia are protected by Solar over 9 years
850
significant companies in Russia are protected by Solar over 9 years
20+ solutions in the product portfolio
IS solutions to organizations from small businesses to the largest enterprises

Solar JSOC, Russia's largest commercial SOC, and Solar MSS, an ecosystem of managed IS services.
Its own product line includes Solar Dozor DLP solution, Solar webProxy web security gateway, Solar NGFW next-generation firewall, Solar inRights IdM system, Solar SafeInspect PAM system, Solar appScreener code analyzer, and others.
Solar Cyberworld and Solar 4RAYS Cyber Threat Research Center are developing a platform for practical training of cyber threat protection skills.
Solar Group in the cyber security market
Protecting the digital future
0
+Attack statistics
Vector of modern cyber attacks

#1
The attackers' goal
Destruction of critical information infrastructure

#2
The attackers' goal
Influencing media infrastructure and embedding anti-Russian political propaganda
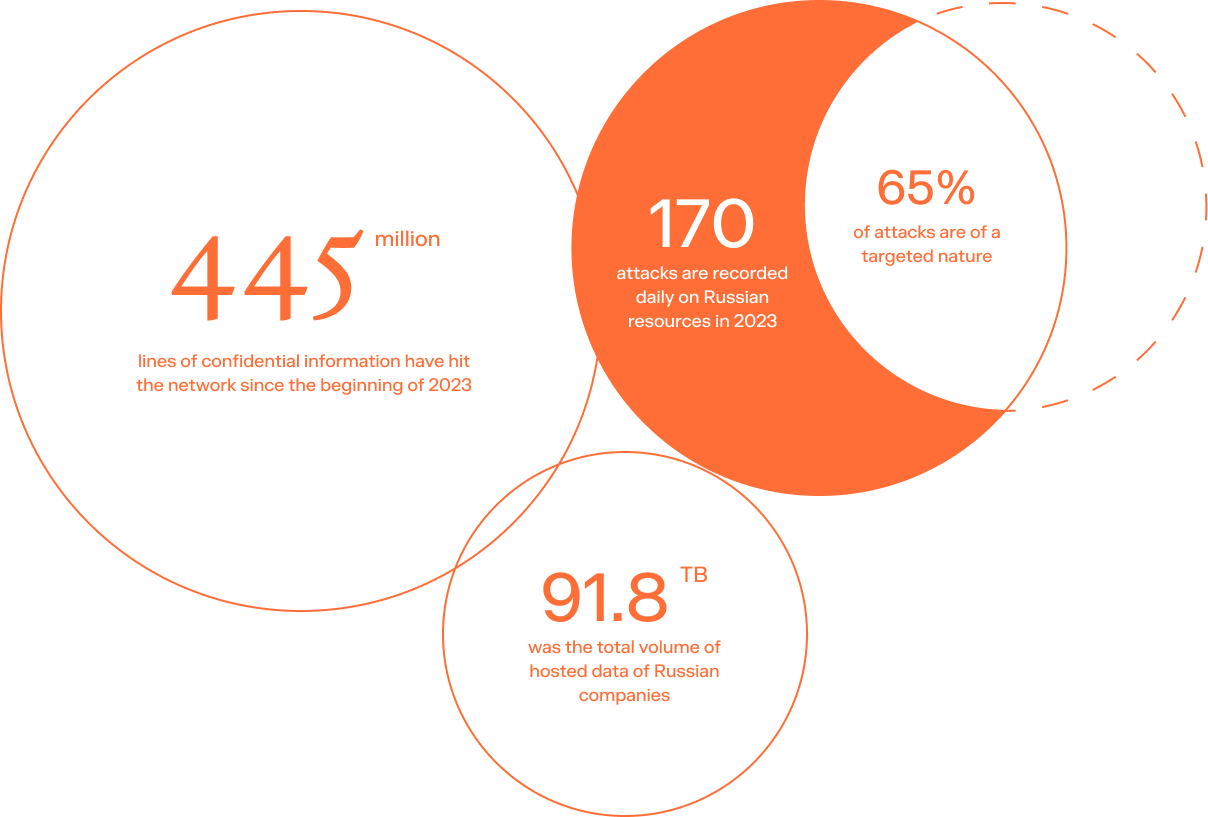
445 million
lines of confidential information have hit the network since the beginning of 2023
91.8 TB
was the total volume of hosted data of Russian companies
170
attacks are recorded daily on Russian resources in 2023
65%
of attacks are of a targeted nature
economic cooperation between the Russian Federation and foreign countries
A comprehensive information security solution - "National Level Cyber Security Platform" for government customers

Public authorities, ministries and agencies

SOCIALLY IMPORTANT OBJECTS

Organizations with critical information infrastructure
"Platform" includes the following components








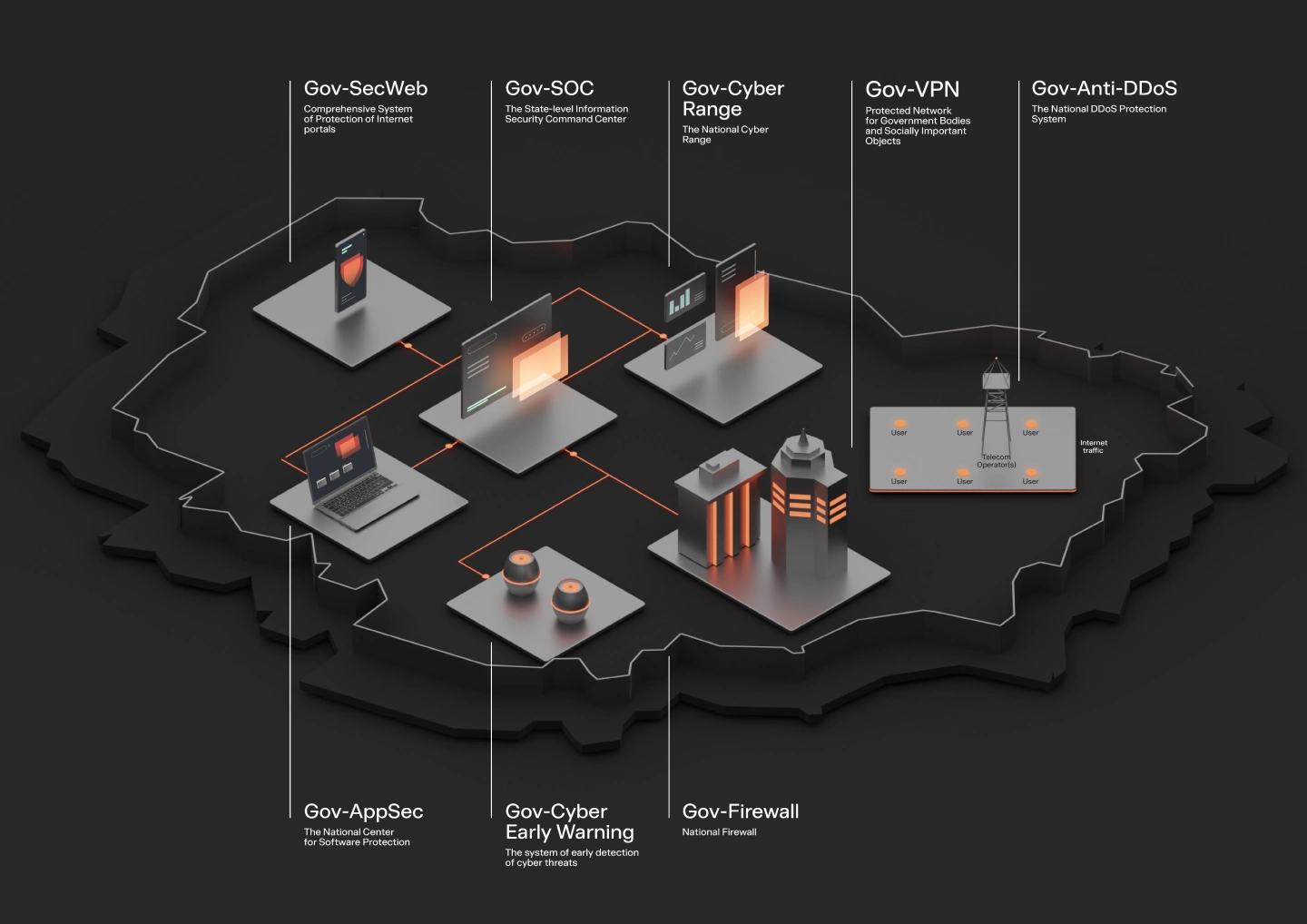
is an operational center that counteracts cyber threats of any level of complexity (coming from both lone hackers and hacker groups supported by state intelligence services) that could potentially lead to attacks of political, terrorist, industrial and criminal nature.
a comprehensive system of protection against Distributed Denial of Services (DDoS) attacks provides reliable protection against massive distributed attacks on the nation's critical infrastructure at the L3/L4 levels of the OSI model. The deployed system neutralizes even the most complex and massive attacks up to 7.6 Tbps and ensures round-the-clock availability of Internet resources to users.
information system for monitoring and management of national Internet traffic, organized to combat terrorism, child pornography, drug trafficking, providing response to massive attacks on the Internet, abuse of its resources, illegal activities, and allows blocking and reducing (degradation) the speed of access to dedicated Internet resources and mobile applications to prevent illegal actions.
a virtual protected network (networks) that provides secure and protected communications for government bodies and socially important objects (e.g., between educational and medical institutions), and is designed to provide secure access to information systems and the Internet. In addition, individual nodes of the Protected Network can be provided with a content filtering service that allows blocking in automatic mode legally prohibited resources and information (for example, extremist materials, pornographic materials, information about drugs and their distribution, calls for suicide, etc.).
providing various government services to the population. This system is a set of organizational measures and technical means aimed at ensuring secure communication between citizens and government agencies on the Internet. The System is protected against any attempts to hack the portal and unauthorized obtaining of personal (personal) data of legitimate users who have access to the System.
is designed to detect previously unknown types and kinds of attacks on organizations' information security systems. The System represents individual servers, a group of servers, or a virtualized automated workstation of users located in different locations across the country and interconnected with each other, to which potential attackers are intentionally provided relatively easy access through pre-prepared "false" vulnerabilities. In the process of attempted penetration, the System identifies attackers and allows to study the methodology and technique of their actions to carry out attacks on information systems, as well as to identify the malicious software and equipment used, in order to practice and apply to "combat" systems methods of countering such attacks.
is a software and hardware complex designed to improve the state's readiness to repel cyber attacks and strengthen national security, including model infrastructures of facilities with critical information infrastructure, and is a platform for conducting cyber exercises of any scale to practice skills of interaction during cyber attacks, training specialists in actual practical skills of defense against cyber attacks.
(hereinafter - Software) ensures the implementation of interrelated organizational and technical activities aimed at the development and use of secure software of any type. Organizational measures include the development of a regulatory framework, definition of approaches, methodology and classification of software, compilation of a unified register of secure software, as well as the creation of accredited laboratories that control software security on a national scale. Technical measures imply the use of special tools for automatic checking of binary and source code for vulnerabilities, bookmarks and undeclared capabilities.
For more information, you can email us at ww.team@rt-solar.ru
Send email